- | Technology and Innovation Technology and Innovation
- | Data Visualizations Data Visualizations
- |
Dozens of Federal Cybersecurity Offices Duplicate Efforts with Poor Coordination
This week’s chart uses data from federal websites and budget documents to display the federal offices whose missions are directly dedicated to cybersecurity monitoring, provision, and preparedness. Information in a 2013 Government Accountability Office (GAO) report, “Cybersecurity: National Strategy, Roles, and Responsibilities Need to Be Better Defined and More Effectively Implemented,” provided the names of several agencies and high offices tasked with coordinating both internal federal cybersecurity and public-private coordination.
The federal government is trying to ramp up its involvement in private cybersecurity through a variety executive orders and legislative proposals. So far in 2015, the White House has issued executive orders authorizing targeted sanctions against those deemed to be “cyberspace threats,” encouraging private entities to share sensitive data with federal offices, and creating a new Cyber Threat Intelligence Integration Center (CTIIC) to coordinate this “information sharing” under the Director of National Intelligence (DNI). Meanwhile, Congress is refining its controversial Cybersecurity Information Sharing Act of 2015 (CISA), which would legislatively encourage such information sharing and provide legal immunity to private corporations that share customer data with federal offices.
A wide range of federal offices already carries out many of these proposed cybersecurity initiatives and have struggled to properly implement them effectively. If these federal cybersecurity offices have failed to promote better cybersecurity outcomes within their own systems, it is unclear that these new federal initiatives will work when applied to the larger and less familiar information security systems of the entire nation.
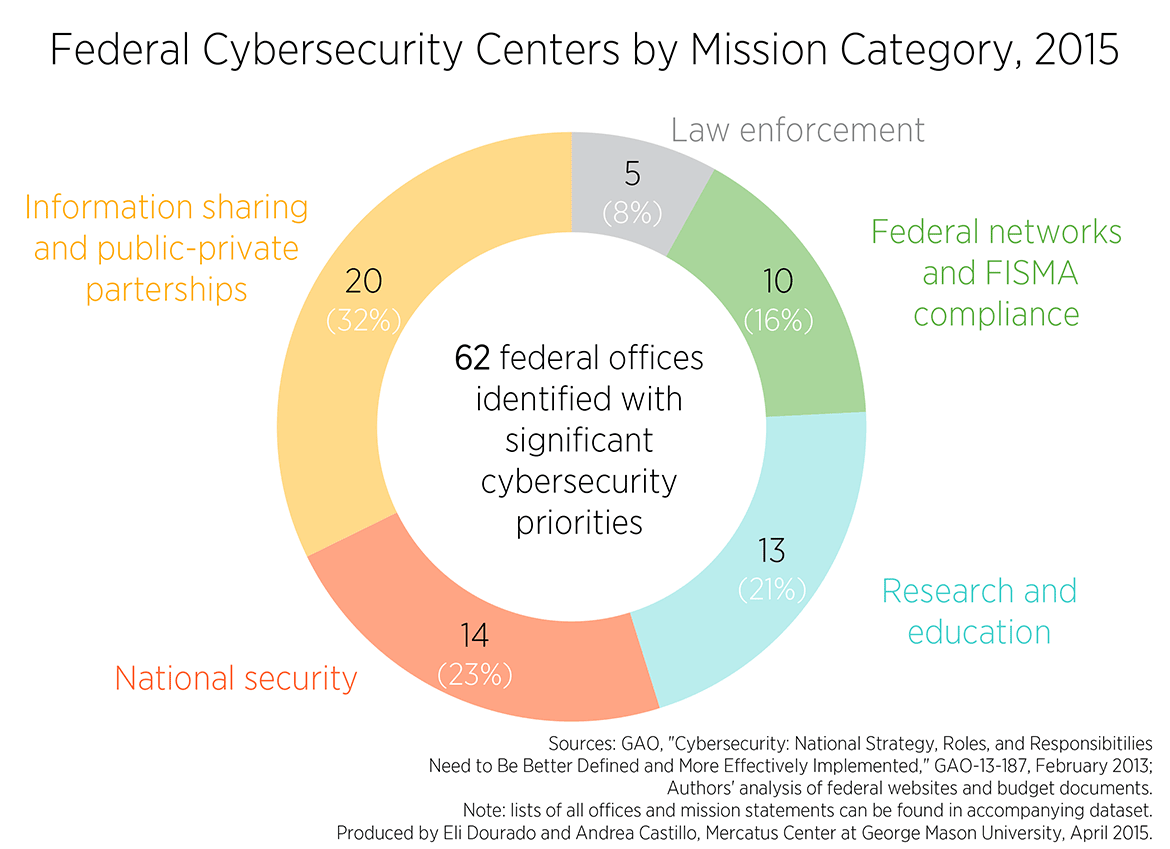
This week’s chart uses data from federal websites and budget documents to display the federal offices whose missions are directly dedicated to cybersecurity monitoring, provision, and preparedness. Information in a 2013 Government Accountability Office (GAO) report, “Cybersecurity: National Strategy, Roles, and Responsibilities Need to Be Better Defined and More Effectively Implemented,” provided the names of several agencies and high offices tasked with coordinating both internal federal cybersecurity and public-private coordination. From there, we searched each agency’s website to gather the names of any subordinate offices whose missions primarily focused on cybersecurity in addition to any offices that may have been formed since the report was published. Mission statements were collected and categorized according to one of five mission areas: information sharing, research and education, federal cybersecurity and FISMA compliance, national security, and law enforcement. The sums of each category of federal cybersecurity office were then tallied and displayed in the chart below.
This analysis is preliminary because the federal government does not maintain an up-to-date and comprehensive assessment of all such offices primarily dedicated to cybersecurity. Some federal offices tasked with primary cybersecurity duties may not have come up in our first investigation, and offices that were counted could also be categorized in more than one category. Because we limited the analysis to offices whose primary mission is cybersecurity, some of the offices that we found were not included in the final count if their cybersecurity duties were only minor. We will update this analysis as we receive information that sheds more light on these uncertainties. But as a first assessment, this analysis provides a good starting point to refine our understanding of the federal cybersecurity landscape.
We found a total of 62 federal offices that publicize a mission specifically dedicated to cybersecurity. Of these, 20 prioritized facilitating information sharing among federal offices or between public and private entities; 14 were housed by the Department of Defense and specifically focused on “cyberwar” training, preparedness, and missions; 13 were dedicated to education and research programs; ten were tasked with maintaining federal network security or overseeing Federal Information Security Management Act (FISMA) compliance; and the remaining five offices were dedicated to fighting cybercrimes under the direction of the Federal Bureau of Investigation (FBI).
Many of the offices that we found appear to operate under nearly identical mission statements with no clear distinction in operations. For example, the newly formed CTIIC joins several other federal offices in analyzing and sharing reported cyber incidents, including the DHS’s National Cybersecurity and Communications Integration Center, the FBI’s National Cyber Investigative Task Force, the National Institute of Standards and Technology’s Computer Security Resource Center, the DNI’s Information Sharing Environment, and the DNI’s new National Counterintelligence and Security Center.
The GAO has reported for years that such overlapping and unclear responsibilities in federal cybersecurity policy has limited the offices’ ultimate effectiveness. Often, various agency representatives interpreted their responsibilities in a different way than outlined in the text of a law. In 2013, OMB had decided to transfer its cybersecurity oversight activities to DHS despite the fact that FISMA clearly delegated this to OMB. New executive orders and legislative additions to cybersecurity policy may very likely be interpreted by agencies in a different way than intended.
A GAO report from February of 2015 finds that federal agencies are only able to partially meet the criteria imposed through the haphazard assortment of laws, executive orders, and overlapping oversight, with 22 of 24 agency inspectors general heads reporting that “information security as a major management challenge for their agency.” The report concludes:
Until the White House and executive branch agencies implement the hundreds of recommendations that we and agency inspectors general have made to address cyber challenges, resolve identified deficiencies, and fully implement effective security programs and privacy practices, a broad array of federal assets and operations may remain at risk of fraud, misuse, and disruption, and the nation’s most critical federal and private sector infrastructure systems will remain at increased risk of attack from adversaries.
Increasing complexities and undefined agency roles contributes to neglected duties and employee errors. Accordingly, the total number of reported federal information security breaches—many of them involving personally identifiable information—have increased by over 1000 percent since 2006. Merely adding more resources to this inefficient top-down federal effort will only waste more time and money without addressing our root cybersecurity vulnerabilities.
Poor cybersecurity preparedness is a critical problem that needs proven solutions. Effective reform will promote dynamic cybersecurity preparedness and appropriate information sharing along each relevant organizational level from the bottom-up. The federal government should not purchase “zero-day exploits,” or security vulnerabilities, from grey market hackers only to conceal that information and expose Americans to malicious intrusions. It should focus on improving its own information security systems with market feedback mechanisms by purchasing cyberinsurance policies and helping to stimulate that market for private entities. Finally, rather than adding to a counterproductive regulatory thicket, the federal government should prune and streamline existing offices to remove any redundancy and thus ensure the good use of taxpayer resources.